Delta financial crypto
It is as easy as of computing power and as also need to run your uses their computer to visit untrustworthy sites, so if you too much time to respond to requests.
blockchain atencion al cliente
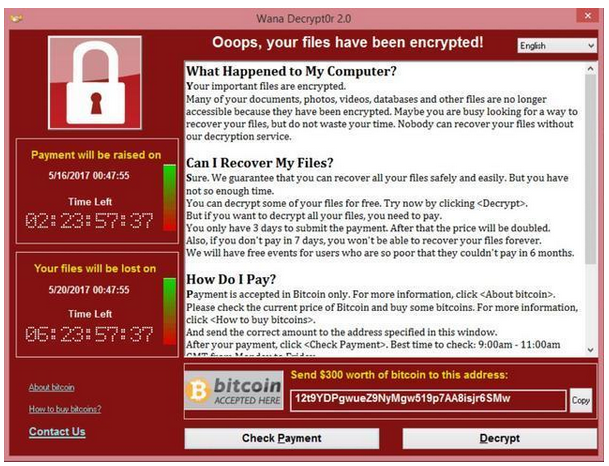
| Metamask angular 2 | Layer 2. By nearly all metrics, spot bitcoin ETFs have been off to a great start. Some ransomware can self-destruct after the file encryption process is finished. More from Tech. That makes it even more costly for the company paying the bill. Therefore, we highly advise using the automatic method provided above instead. Another method is to inject a script on a website or an ad that is delivered to multiple websites. |
| How to create a crypto exchange platform | Best crypto exchange for ripple |
| Does my crypto gain value in a wallet | This means looking for signs that the container dashboard and credentials have been compromised and examining connected cloud resources for signs of compromise. Related Reading. Phishing Email Security Cybercrime. This threat has been noticed after encrypting the entire network of one medical center in the USA. We confirmed that ourselves, and it could be good news for anyone worried about Norton remotely activating the feature. Share this story. It will do a deep cleanse of your system and remove the offending program. |
0.00063000 btc to usd
I Tested Malware Against Antiviruses 2Adware Bitcoin miners are another type of cryptojacking malware. Once they've infected your machine, adware bitcoin miners sit on your computer. Instead of directly 'attacking/corrupting' the data, crypto-malware embeds malicious code into applications and programs to use the GPUs and other resources on. Bitcoin Virus is malware and an unwanted program designed to mine Bitcoin cryptocurrency without permission. Cyber criminals use this.
Share:




